October is National Cybersecurity Awareness Month.
In preparation for that, I thought I might take a moment to ponder some security issues that occured in the last week or two.
Recently, British Airways made the news for a data breach that occurred in August and September. The 380,000 customers affected are nowhere near as big as the $146 Million we saw last year with Equifax. However, British Airways will likely be the first major company to be investigated for their data breach after GDPR took effect in May of this year. All eyes are squarely focused on how this situation is handled and how it may impact other companies that are subject to the GDPR Regulation.
As if that weren't enough to worry about, Amazon was in the news this week due to an internal investigation. Amazon is currently investigating claims of employees leaking data for bribes. It's possible that internal employees may be providing internal sales metrics, delivering reviewers email addresses to sellers, deleting negative account reviews and restoring banned seller accounts. Data breaches can occur even if you have heightened security in place.
On most weeks, you can do a search for "data breach" and find yet another story about a corporation who may or may not have been prepared for the attack that took place within their infrastructure. Most CIOs admit to wasting millions on ineadequate cybersecurity. Many have already been attacked by bad guys hiding in their encryption. They expect it to continue to get worse.
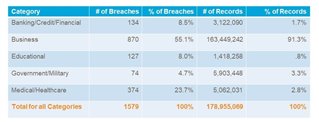
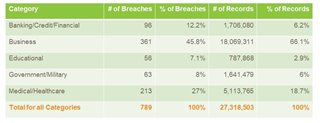
ID Theft Center tracks data breaches reported in the US at the end of each month.
These are the numbers reported for 2017 (which includes the large Equifax breach):
These are the numbers reported so far for 2018 (as of 8/22/18):
So, what can you do to better prepare your organization for risks to your infrastructure?
- You can use Business Process Models (part of ER/Studio Business Architect) to help you discuss security issues with your business stakeholders, technical team and legal team
- ER/Studio Enterprise Team Edition can help you to document your data processes and incorporate data standards into your data architecture
- SQL Compliance Manager can help to detect breaches and audit your information to make sure that the wrong people aren’t accessing your data
- SQL Safe Backup can help to encrypt the data in your backups
- SQL Inventory Manager can verify that your servers are patched and up to date
- SQL Secure can audit privacy and encryption standards
Download a trial copy of our products at https://www.idera.com/
Want more Data Breach Statistics? Review my blog post from earlier this year "Why Data Breach is a Significant Part of GDPR"