The increased focus that organizations are placing on their data resources has put a premium on their use of database technology. Making productive...


The increased focus that organizations are placing on their data resources has put a premium on their use of database technology. Making productive...
In Windows PowerShell, updating help used to require Administrator privileges due to a design flaw: help had to be stored in the location where the...
In the previous script we came up with a one-liner that checks which profile scripts actually exist. This solution works per host only, though,...
Precise now supports the latest Oracle 19.7 patch on Linux and the Oracle 19.8 patch on Solaris. The latest patch from Oracle for Oracle 19C on...

Heuristics and normalization are the goals of all databases. Heuristics refers to a trial-and-error method of problem-solving used when an...

Protecting enterprise data resources has never been more important. The large quantities of data that many organizations store present an inviting...
PowerShell uses up to four profile scripts. When they exist, PowerShell silently executes any content when it launches. It’s important to know...

Most websites that provide any degree of usefulness or functionality make use of one or several databases. Whether the site is designed to simply...

Infographics provide a method of conveying a lot of information in a condensed and visual form. They are a widely-used way of capturing an...
Profile scripts work like autostart scripts in PowerShell. They do not need to exist, but if they do, PowerShell executes its content silently...

One of the appeals of using SQL Server as a database platform is the functionality and productivity that can be enjoyed through the use of the SQL...
Be careful when using $env:userprofile or $home to create paths to user files. When a Windows box is set up for OneDrive, the documents folder may...
The Get-EventLog cmdlet provides easy access to event log entries in the primary Windows event logs, however it neither can access the many...

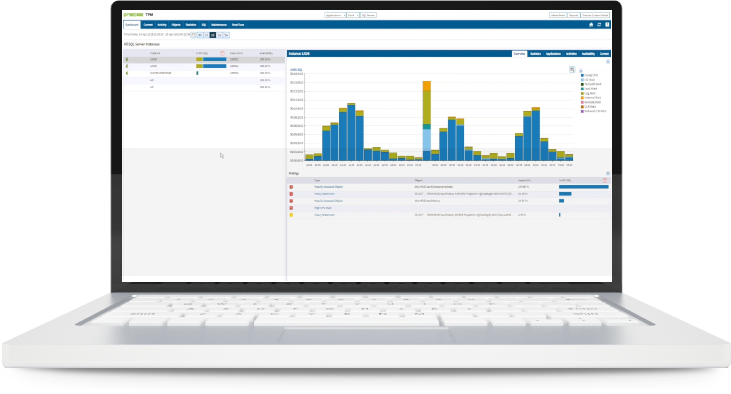
In the quest for optimal database performance, DBAs need to leave no stone unturned. After keeping the data resources in their systems secure, there...
PowerShell remoting maintains a list of trusted IP addresses and/or machine names on the client side (the machine that issues the command and...

Data can be skewed by its nature. How can you tell if you have skewed data in your database? And if you do, how do you handle it when writing...

For those readers attracted to the title of this post in the hopes of finding a new way to cope with your vehicle’s windshield wipers in a...
The PowerShell ISE built into Windows works with Windows PowerShell only and is stuck at PowerShell version 5.1. Typically, when you want to use an...

Securing an organization’s computing environment from malicious external actors is a critically important and extremely complex undertaking....

It would be nice if there existed some methodology that enabled DBAs to fully protect their SQL Server environment from hackers, malware, and...
In PowerShell 7, there is a new set of variables all starting with “Is”. They help you understand the environment in which your script...

Dr. Codd’s original relational algebra had eight basic operations. Since relational database management systems are based on set theory, the...

Organizations that make efforts to secure MySQL databases can massively mitigate the risk of suffering a data breach. The escalating number of data...
You can use PowerShell to enable and disable real-time antivirus protection provided you are running with full Administrator privileges. Temporarily...