Anthem Inc. – 80,000,000 records stolen; Sony Pictures – 100 terabytes of data stolen; JP Morgan Chase – 70,000,000 records stolen; and EBay –...
Anthem Inc. – 80,000,000 records stolen; Sony Pictures – 100 terabytes of data stolen; JP Morgan Chase – 70,000,000 records stolen; and EBay –...
Precise provides a rich toolset to monitor Oracle Exadata. Oracle Exadata provides significant improvements in accessing the data in tables quickly...
If you must put a credential object in your script, here is a way how you can convert a secure string into encrypted text: $password = Read-Host...
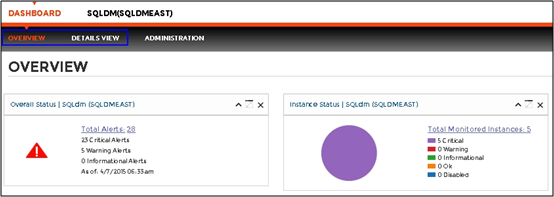
We are pleased to announce that SQL Diagnostic Manager 9.1 will soon be available for beta testing. Please note that this will be pre-release code...
RAD Studio XE8 provides you with the tools to rapidly design, build, and deploy connected apps that deliver innovative IoT solutions. The new Beacon...
To quickly get a list of all drive letters in use, try this: #requires -Version 1 [Environment]::GetLogicalDrives() The result is a list of all...
PowerShell 3.0 and later In a previous tip we explained how you can use the Windows product ID stored in the Windows Registry to encrypt some text...
PowerShell 3.0 and later To store secret information, you can use a SecureString object and save it to disk. PowerShell automatically takes the user...
Tinker, Tailor, Developer, DBA is not intended as a pitch on a slightly less harrowing book or movie than the John Le Carre classic. ...
Microsoft Exchange 2013 To find the number of mailboxes, simply use the Exchange cmdlets and have Measure-Object count the results: Get-Mailbox...
Last weekend I had the pleasure of attending SQL Saturday 375 in Mountain View, California. This was my second time attending this particular event,...
PowerShell 2.0 and later When you create PowerShell functions with parameters, make sure you tell PowerShell what kind of values the parameter...
All Versions Cmdlets can declare how severe their impact is. Typically, cmdlets that make changes to the system that cannot be undone will have an...