Ever wondered why your CPU load is so high at times, or why black windows open up for a split second? Then check your event log for program...
database-tools
Finding Logon Events
Provided you have Administrator privileges, here is a quick and easy way of dumping all login events. This way you can find out who logged in to a...
Resolving URLs
Often, URLs redirect to the final URL, so if you’d like to know where a given URL really points to, use a function like this: function...
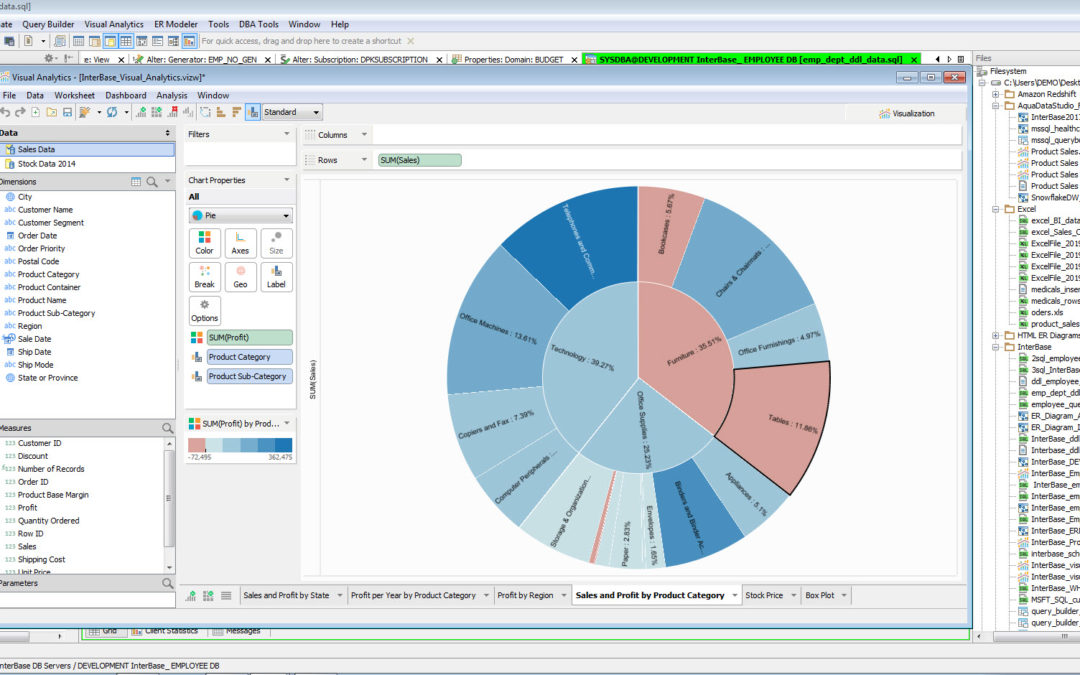
Access InterBase and Snowflake with Aqua Data Studio
Last month, Lisa Waugh announced the release of the latest version of Aqua Data Studio (ADS). Version 20.0 expands the platform coverage of this...
Finding Size of Download
When you download files from the internet and use PowerShell, you may want to find out how long the download will take. While you can check the size...
Solutions for the Cloud – Virtualization
Welcome to our latest weekly blog series, Solutions for the Cloud. This series will focus on central concepts and benefits related to the cloud and...
Detecting Key Press
Sometimes it would be nice if a script was able to detect a key press without interfering with the script and its inputs. This way, you could add...
June #SQLChat – Optimizing SQL Server Indexes
SQL Server indexes can improve SQL Query performance when done correctly - but how do you create an optimal set of indexes? Join IDERA...
Using FileSystemWatcher Asynchronously
In the previous tip we looked at the FileSystemWatcher object and how it can monitor folders for changes. To not miss any changes, however, an...
Using FileSystemWatcher Synchronously
Here is a chunk of code illustrating how PowerShell can use the FileSystemWatcher to synchronously watch a folder including subfolders for file...
Using Default Credentials for Proxy
When your company uses an authenticated proxy, PowerShell may not always be able to contact the Internet. You may have to instruct the web proxy to...

Announcing the GA Release of SQL Secure 3.3
We’re excited to announce the release of SQL Secure 3.3. SQL Secure is an auditing and security tool for SQL Servers. It helps...
PowerShell 7
Today we are not talking about code but about PowerShell in general. Microsoft has announced that the next release of PowerShell is called...
RSAT Tools Built-In
The Remote Server Administration Tools (RSAT) used to be an external download that added two important PowerShell modules: ActiveDirectory and...
Searching Files Using Index Search
Windows Indexing indexes most files in your user profile and drives the fast file search in File Explorer. PowerShell can access the same mechanism....
Turn on Streaming for Loops
PowerShell comes with a number of looping constructs. These looping constructs cannot stream, so you cannot pipe the results to other cmdlets and...
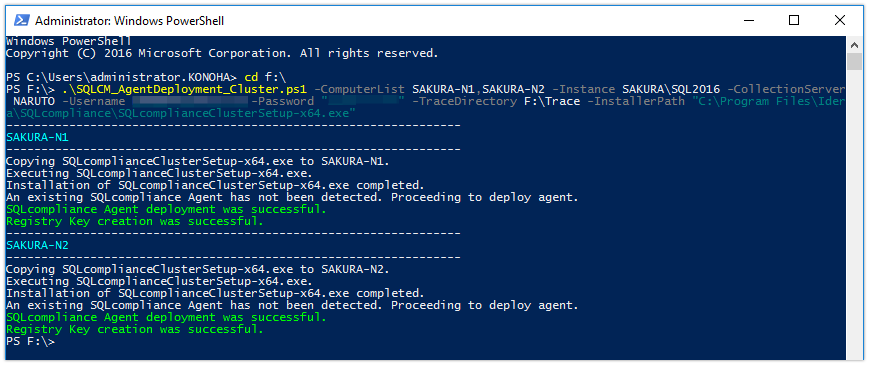
Deploying the SQLcompliance Agent in a Failover Cluster Environment Using a Powershell Script
Background A few months ago, I spoke to one of our SQL Safe Backup customers that had a very large SQL Server environment. In an effort to...
Marking Scripts for PowerShell Core or Windows PowerShell
As you probably know, there are two breeds of PowerShell: Windows PowerShell ships with Windows operating systems and is based on the full .NET...
Controlling Audio Volume and Mute Status
To adjust an audio volume and mute/unmute the speaker, PowerShell can use C# code and access API functions like this: Add-Type -TypeDefinition...

Announcing General Availability of Aqua Data Studio 20.0!
On behalf of the entire Aqua Data Studio team, we’re excited to announce the release of Aqua Data Studio version 20.0 with major enhancements...
Checking for Bad (Insecure) Passwords (Part 2)
In the previous tip we explained how you can use web services to safely test passwords and find out whether they have been compromised before....

How to look for extra funding for database administration tools
It is difficult for database administrators to run their databases efficiently and effectively without proper funding. Whether you are asking for...
Checking for Bad (Insecure) Passwords (Part 1)
Complex passwords are not necessarily safe. For example, “P@ssw0rd” is a very complex password, however extremely insecure. That’s...
Specifying Bit Flags Smart
In the previous tip you have seen how you can enable all SSL security protocols in PowerShell to connect to web services and web sites:...