In the previous tips, we took a deep look at how PowerShell 5 script block logging works: in a nutshell, when enabled, all PowerShell code that...
database-tools
Finding Secret Passwords in Memory
Some scripts may leave variables with sensitive information behind. This can happen by accident, when the global scope is used, or when users call...
Outputting Data to HTML Reports
Here is a super easy and useful PowerShell function called Out-HTML: function Out-HTML { param ( [String] $Path = "$env:temp\report$(Get-Date...
Stealing Sensitive Data from PowerShell Functions
Frequently, PowerShell functions work with sensitive information, i.e. log-on information including passwords, and store this information in...

IDERA Honored in DBTA’s “Big Data 50” List
We’re proud to announce that for the second straight year IDERA was named to the “Big Data 50” list published annually by...

October #SQLChat: Making the Most of Conferences – From Training to Networking
So you're attending a training conference next month. Maybe you're a first timer, maybe this is your 10th year. Making sure you...
Handling Credentials as Parameters
Credentials are objects that contain a user name and an encrypted password. If your PowerShell functions should be able to accept credentials,...
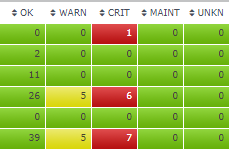
Attention Operational DBAs
Uptime Database Infrastructure Monitor triages large environments so that you can quickly determine what needs your immediate attention, Database...
Resolving Mapped Drive
Ever wanted to know the original URL behind network drives? Here is an easy PowerShell way: # make sure the below drive is a mapped network drive #...

Data Breaches Are Common – Are You Prepared?
October is National Cybersecurity Awareness Month. In preparation for that, I thought I might take a moment to ponder some security issues...

The Simple 3-2-1 Rule for Backups
Earlier this month, one of Microsoft's Azure data centers encountered an outage that impacted customers worldwide. Microsoft recently...
Downloading Data with BitsTransfer in the Background
Downloading very large files can be a challenge because the download process may take longer than a machine is turned on. With BitsTransfer, you can...
Downloading Data via SSL and BitsTransfer (Sync)
A very convenient built-in way to download files, even with SSL connections, is Start-BitsTransfer. It also sports a progress bar that shows the...
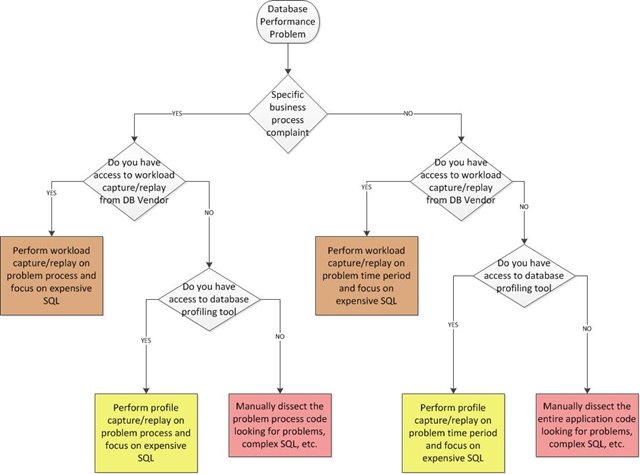
Fixing Database Performance Problems
(content originally posted by Bert Scalzo on 3/8/2017) There is no such thing as the perfect database. No matter how hard the DBA may try, something...
Downloading Data via SSL and Invoke-WebRequest
Invoke-WebRequest can download files for you but may struggle with HTTPS URLs. To use SSL connections, you may have to change a default setting....
Finding Disabled GPOs
Here is a quick one-liner that dumps all Group Policy objects that have all settings disabled: Get-Gpo -All | Where-Object GpoStatus -eq...
Browsing All Event Logs
Get-EventLog always requires you to specify exactly one event log via -LogName. You cannot use wildcards, and you cannot browse all event logs at...
Creating Event Log Reports
You probably have used Get-EventLog frequently to dump event log information, for example: PS> Get-EventLog -LogName System -EntryType Error...
Keyboard Shortcuts for PowerShell Console
The PowerShell console starting in version 5 ships with a module called PSReadLine which does much more than just coloring command tokens. It comes...
Using SSH from PowerShell
PowerShell 6 (PowerShell Core) finally ships with SSH support: you can use SSH to connect to non-Windows machines for PowerShell remoting...
Managing Lenovo BIOS Settings (Part 4)
In the previous tip we showed how you can read and change BIOS settings for Lenovo computers. This was the code to disable WakeOnLan, for example:...

Five reasons SQL Server health checks are life savers
SQL Server health checks have garnered a great deal of notoriety over the last five years. What was initially a niche offering more than ten years...

How can DevOps help database teams improve software delivery?
DevOps Research and Assessment (DORA) published a detailed report on the state of DevOps entitled "Accelerate: State of DevOps 2018: Strategies...
Managing Lenovo BIOS Settings (Part 3)
In the previous tip we explained how to manage Lenovo BIOS settings from PowerShell. Typically, there are single settings that need to be managed....